This configuration only provides only the minimum to get the Traefik Dashboard running with Let’s Encrypt-driven SSL encryption and user authentication. It also redirects all HTTP requests to HTTPS in order to avoid insecure access to the Dashboard and other services.
Let’s encrypt is used with the HTTP-01 challenge. This means that Traefik MUST be reachable by Port 80 from the Internet.
In order to install docker & docker-compose, see How to install docker and docker-compose on Ubuntu in 30 seconds.
First prepare the directory (/var/lib/traefik):
sudo mkdir /var/lib/traefik
sudo chown -R $USER: /var/lib/traefik
cd /var/lib/traefik
mkdir acme conf
Now create docker-compose.yml:
version: "3.3"
services:
traefik:
image: "traefik:v2.3"
container_name: "traefik"
command:
- "--api=true"
ports:
- "80:80"
- "443:443"
- "8080:8080"
volumes:
- "/var/run/docker.sock:/var/run/docker.sock:ro"
- "./acme:/etc/traefik/acme"
- "./traefik.toml:/etc/traefik/traefik.toml"
- "./conf:/etc/traefik/conf"Now create the main traefik.toml configuration file:
defaultEntryPoints = ["http", "https"]
[api]
dashboard = true
# You can create config files in /var/lib/traefik/traefik.conf and Traefik will automatically reload them
[providers]
[providers.file]
directory = "/etc/traefik/conf/"
watch = true
# Change this to INFO if you don't want as much debug output
[log]
level = "DEBUG"
[entryPoints.web]
address = ":80"
[entryPoints.web.http]
[entryPoints.web.http.redirections]
[entryPoints.web.http.redirections.entryPoint]
to = "websecure"
scheme = "https"
[entryPoints.websecure]
address = ":443"
[certificatesResolvers.letsencrypttls.acme]
# TODO Add your email here
email = "[email protected]"
storage = "/etc/traefik/acme/acme.json"
[certificatesResolvers.letsencrypttls.acme.httpChallenge]
entryPoint = "web"
Now we need to create the API config file in conf/api.toml:
[http.routers.traefik-api]
# TODO: Set your domain here !!!
rule = "Host(`traefik.example.com`)"
service = "api@internal"
middlewares = ["auth"]
[http.routers.traefik-api.tls]
certresolver = "letsencrypttls"
[http.middlewares.auth.basicAuth]
# TODO Add your admin user & password here, generate e.g. using https://wtools.io/generate-htpasswd-online
users = [
"admin:$1$ySFBr~_y$GsKgEasDQkpCX8sO8vNia0",
]
Don’t forget to change your email address and the domain name in the config files (marked by TODO). Ensure you have setup all DNS records correctly so that your domains points to the server running Traefik!
Now it’s time to startup Traefik for the first time:
docker-compose up
Traefik will take a few seconds to automatically generate the Let’s Encrypt certificate for your domain. Once you see a message like
traefik | time="2020-09-20T23:48:30Z" level=debug msg="Certificates obtained for domains [traefik.mydomain.com]" providerName=letsencrypttls.acme routerName=traefik-api@file rule="Host(`traefik.mydomain.com`)"
the certificate is available and loaded automatically.
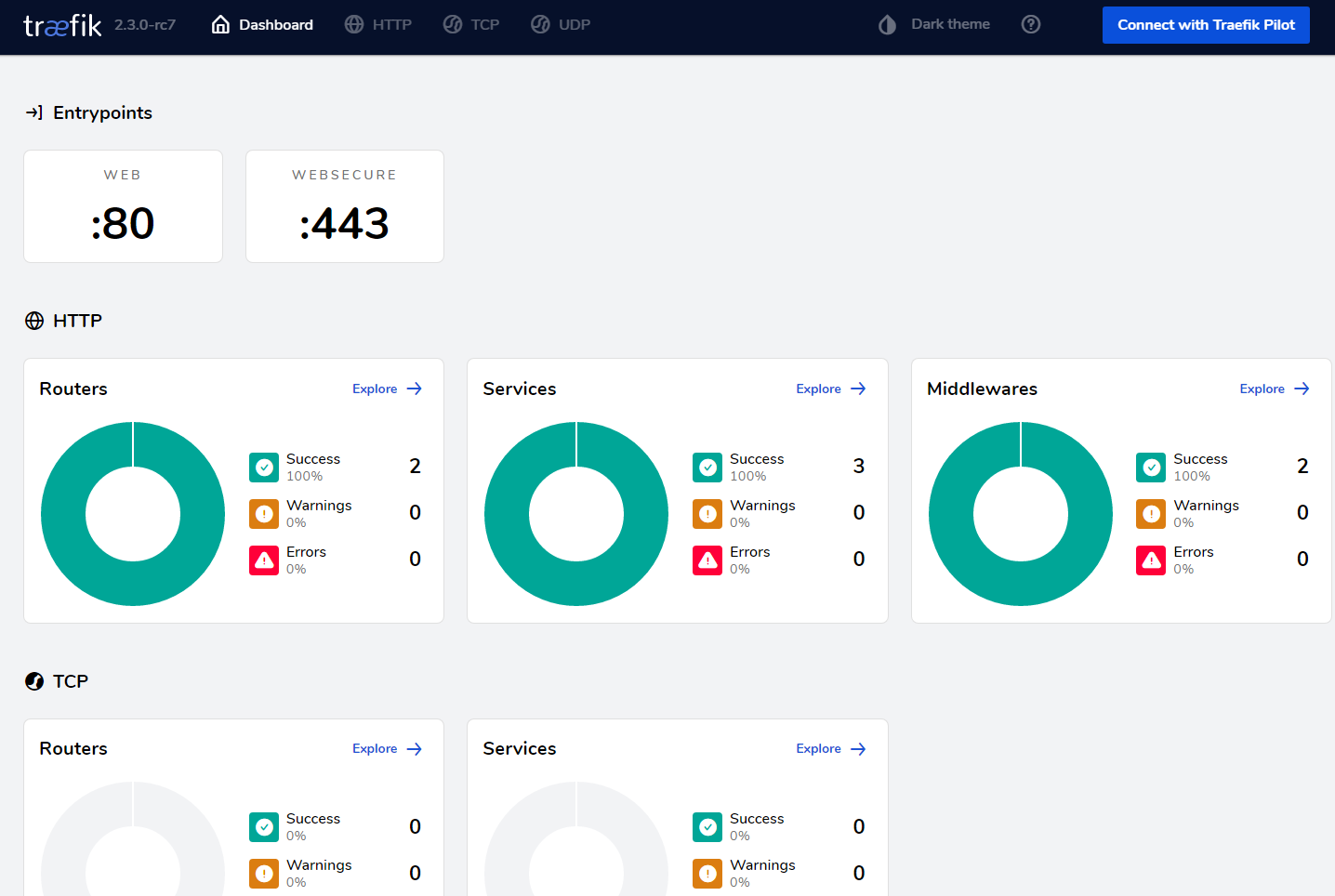
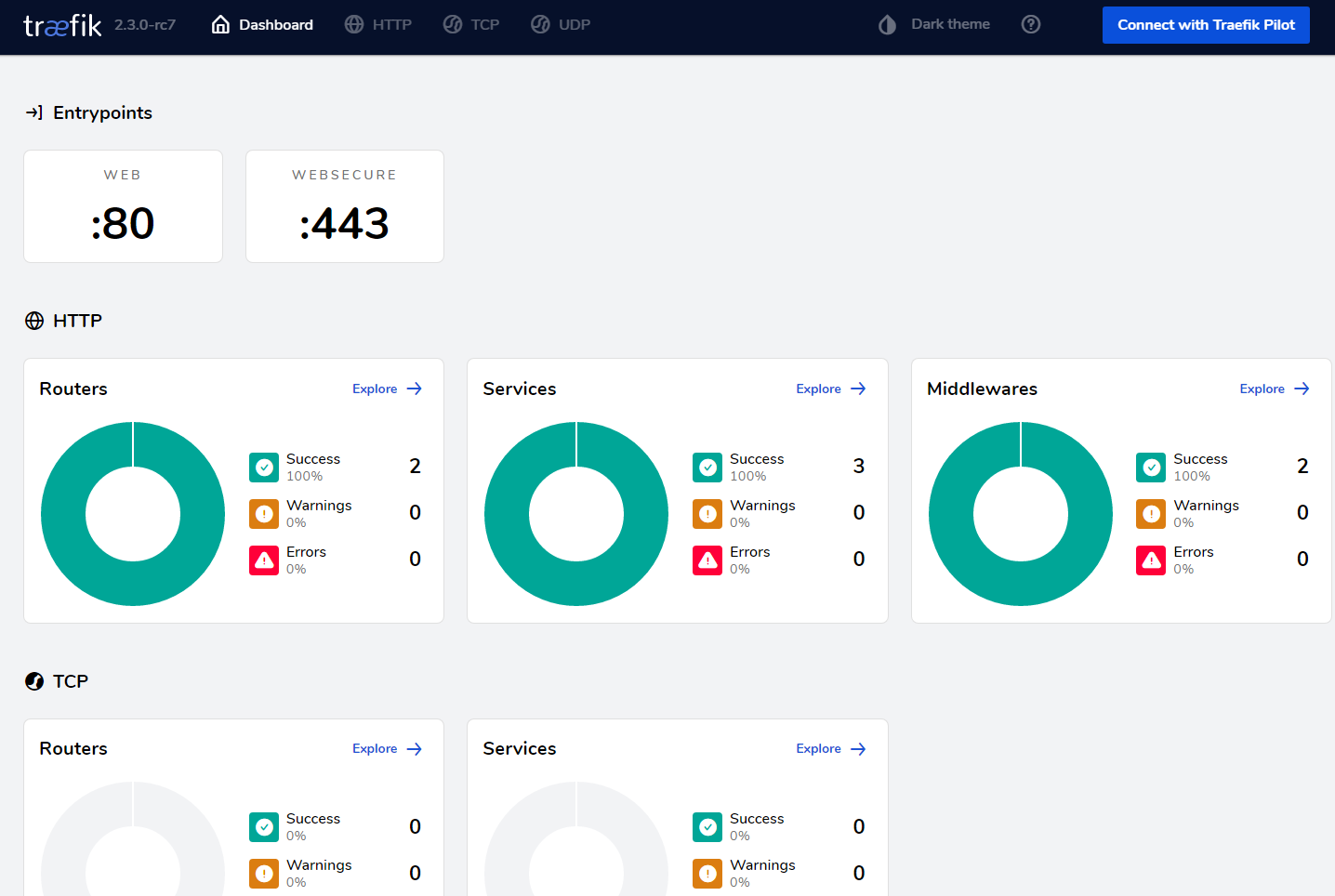
Now you can go to https://traefik.mydomain.com/ , login with the username and password you have generated and check out the dashboard.
If desired, you can also setup a systemd service to automatically start Traefik on boot (generated using docker-compose systemd .service generator). In order to do this, first stop the running docker-compose instance using Ctrl-C if you still have the terminal open and docker-compose down.
Now add this as /etc/systemd/system/traefik.service:
[Unit]
Description=traefik
Requires=docker.service
After=docker.service
[Service]
Restart=always
User=root
Group=docker
WorkingDirectory=/var/lib/traefik
# Shutdown container (if running) when unit is stopped
ExecStartPre=/usr/local/bin/docker-compose -f docker-compose.yml down -v
# Start container when unit is started
ExecStart=/usr/local/bin/docker-compose -f docker-compose.yml up
# Stop container when unit is stopped
ExecStop=/usr/local/bin/docker-compose -f docker-compose.yml down -v
[Install]
WantedBy=multi-user.target
and run
sudo systemctl enable traefik.service
sudo systemctl start traefik.service